Created: 8-13-17
Updated: 8-13-17
Hey guys,
So here is a write up on how to setup Terminal Services in a Sonicwall Firewall.
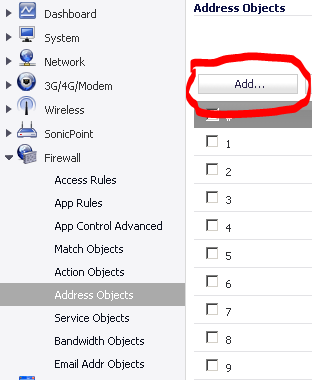
So let’s get started. Log into your Sonicwall and go to the “Firewall” section and click on “Address Objects” and press “Add” as shown below:
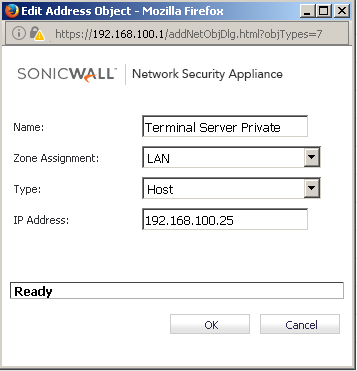
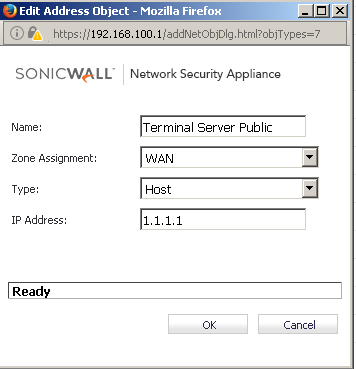
Now we need to create two address objects, one will be the internal (private) IP address of the Terminal Server Master which is the primary round-robin distribution server of the TS Farm, as discussed in this blog article, and the other address objects is with the external (public) IP address of Terminal Server that will be reachable by your remote users.
It’s worth noting, this externally facing IP address will need to be mapped to your external registrar’s DNS server if you want to resolve the Terminal Server by name, such as cloud.matrix.com. On your external registrars DNS server for your domain, here caled “Matrix”, you would need to make a A record for “cloud” mapped to one of the external (public) IP addresses provided by your ISP. In the picture below, let’s say it’s 1.1.1.1, the other IP address is a (private) LAN-based IP address.
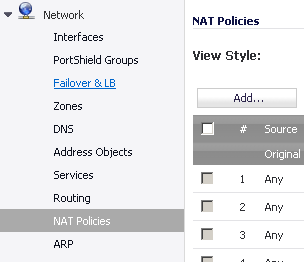
Now that we have this object created,we can proceed to the “NAT Policies” that will need to be created to translate “Public into Private” and “Private into Public” addresses.
Click on the “Network” Section, and click on “NAT Policies”, and press the “Add” button, as shown below:
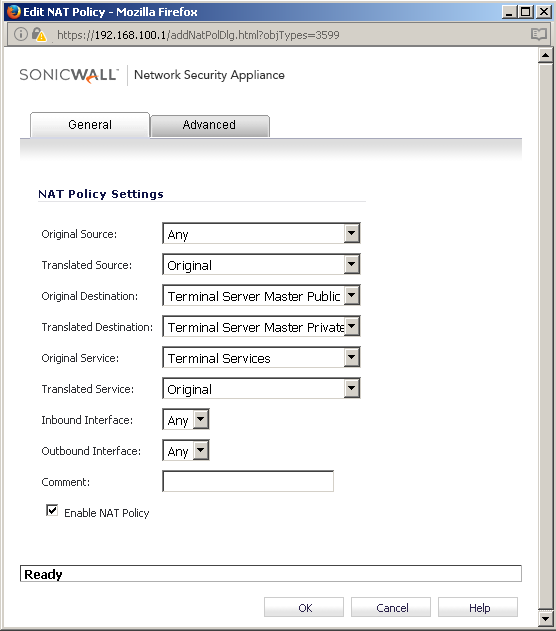
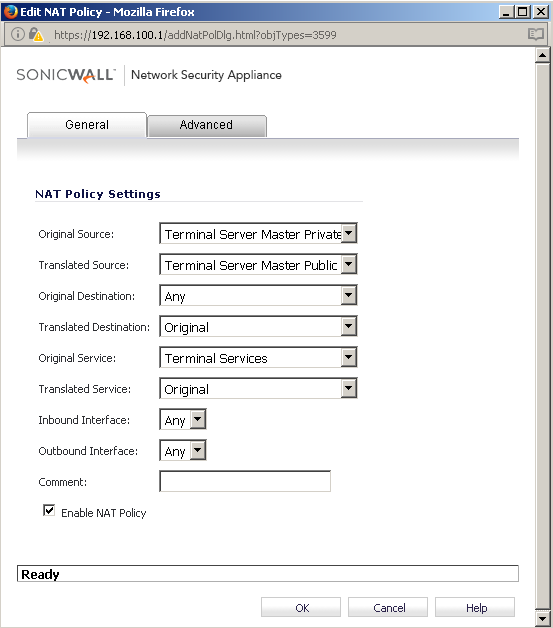
Now in this part, we are going to create two rules, as shown below, right now kind of doing laundry, so I’ll come back and finish this later, just make sure to copy these exactly as they are, they need to be a mirror of each other. One is inbound traffic and one is outbound traffic, once you connect to the TS Farm, you should have a rule setup that allows that traffic to be NAT’d in the other direction too. 🙂
Now that we have created the “NAT Policies”, we can proceed to the creation of “Access Rule” to define the rule in the Firewall.
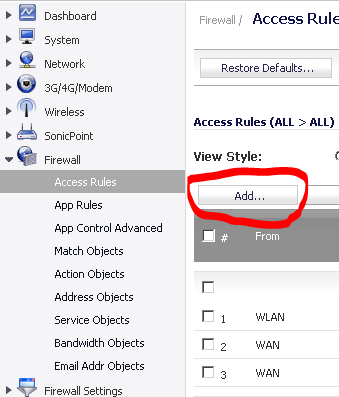
Click on the “Firewall” section, and click on “Access Rules” and press the “Add” button, as shown below:
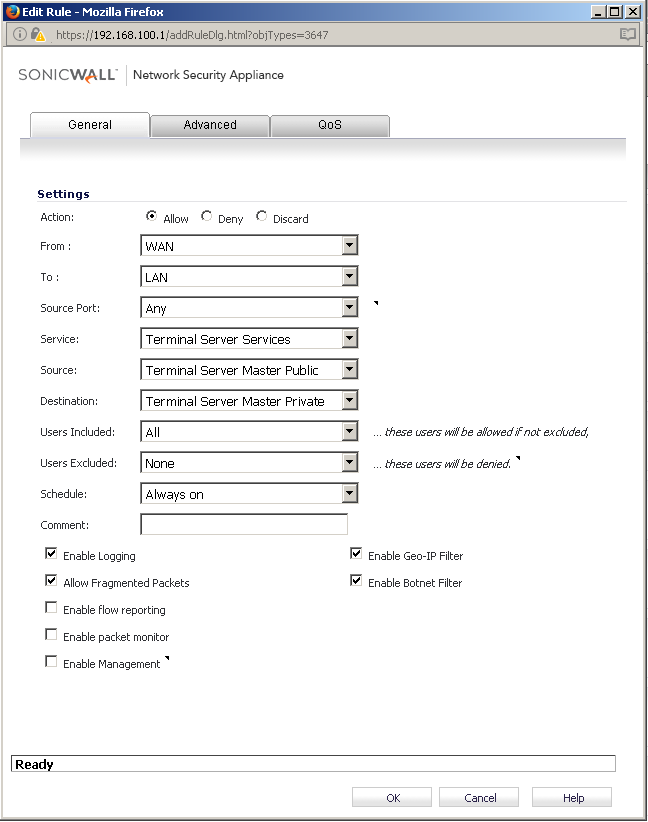
Once you press the “Add” button, you will need to selected “WAN” as the “From”, “LAN” as the “To”, the source port can be a “ANY”, the “Service” will use a predefined field called “Terminal Server Services” which uses the default 3389 (if you use a different port, you will need to make a custom service group rule), the “Source” will be the “Terminal Server Master’s Public” IP address that you defined from your block of IP address from your ISP, and then finally your “Destination” will be the “Terminal Server Master’s Private” IP Address that is defined on your LAN Subnet. Finally, this should be set as an “Allow” for the action. Press “OK” and the rule will be applied to the Firewall Rules.
Now after all of this is setup you should be able to resolve your internal TS Farm from external locations either via the public IP Address or the name resolution setup mapped to that public IP address.
I hope this write up has been helpful to you guys and it serves you well. 🙂